We need you 2/5
Category: Forensics
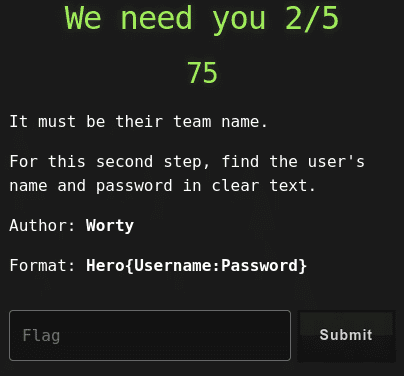
75 points
It must be their team name.
For this second step, find the user’s name and password in clear text.
Author: Worty
Format: Hero{Username:Password}
Solution
This is continuation of We need you 1/5 challenge.
This time the goal is to get username and password.
I’ve retrieved hashes as below.
~/git/volatility3/vol.py -f capture.mem windows.hashdump
Volatility 3 Framework 1.0.1
Progress: 100.00 PDB scanning finished
User rid lmhash nthash
Administrateur 500 aad3b435b51404eeaad3b435b51404ee 31d6cfe0d16ae931b73c59d7e0c089c0
Invité 501 aad3b435b51404eeaad3b435b51404ee 31d6cfe0d16ae931b73c59d7e0c089c0
Razex 1000 aad3b435b51404eeaad3b435b51404ee 78d9c7e905c695087ee3baa755ce43e4Saved them to file and tried dictionary attack with hashcat.
hashcat.bin -m 1000 -d 1 -a 3 hashes.txt rockyou.txtAfter a while…
hashcat.bin -m 1000 -d 1 -a 3 hashes.txt --show
78d9c7e905c695087ee3baa755ce43e4:liverpoolfc123Flag
Hero{Razex:liverpoolfc123}