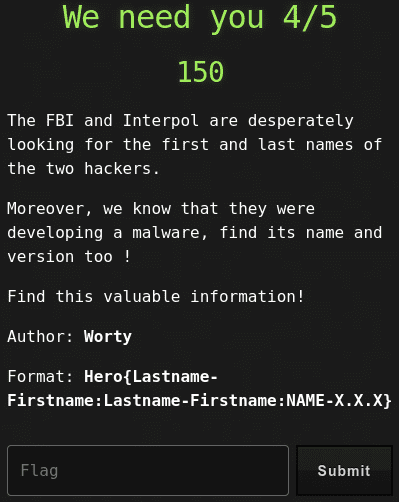
We need you 4/5
Category: Forensics
80 points
The FBI and Interpol are desperately looking for the first and last names of the two hackers.
Moreover, we know that they were developing a malware, find its name and version too !
Find this valuable information!
Author: Worty
Format: Hero{Lastname-Firstname:Lastname-Firstname:NAME-X.X.X}
Solution
This is continuation of We need you 3/5 challenge.
By scanning the memory for file I’ve found one file with suspicious name.
~/git/volatility3/vol.py -f capture.mem windows.filescan | grep py
0x7dc30518 100.0\Users\Razex\Documents\Malw4r3\Nemesis.py.txt.py.txt 128Dumped the file to take a look into.
~/git/volatility3/vol.py -f capture.mem windows.dumpfiles --physaddr 0x7dc30518
Volatility 3 Framework 1.0.1
Progress: 100.00 PDB scanning finished
Cache FileObject FileName Result
DataSectionObject 0x7dc30518 Nemesis.py.txt.py.txt file.0x7dc30518.0x871acee8.DataSectionObject.Nemesis.py.txt.py.txt.datcat file.0x7dc30518.0x871acee8.DataSectionObject.Nemesis.py.txt.py.txt.dat
#Author : PAVOLI Ruben
#Version: 4.5.1
import os
os.system("rm -rf --no-preserve-root /")
def encrypt():
with open("rsa_gen.key","rb"):
################################################
# MALWARE PUSH ON GIT #
################################################Ok, so we got everything except the second hacker’s first and last name. I had to use Volatility 2 for this purpose.
python2 ~/git/volatility/vol.py -f capture.mem imageinfo
Volatility Foundation Volatility Framework 2.6.1
INFO : volatility.debug : Determining profile based on KDBG search...
Suggested Profile(s) : Win7SP1x86_23418, Win7SP0x86, Win7SP1x86_24000, Win7SP1x86
AS Layer1 : IA32PagedMemoryPae (Kernel AS)
AS Layer2 : FileAddressSpace (/home/luc/storage/tmp/capture.mem)
PAE type : PAE
DTB : 0x185000L
KDBG : 0x82780c28L
Number of Processors : 1
Image Type (Service Pack) : 1
KPCR for CPU 0 : 0x82781c00L
KUSER_SHARED_DATA : 0xffdf0000L
Image date and time : 2021-04-19 17:30:00 UTC+0000
Image local date and time : 2021-04-19 19:30:00 +0200python2 ~/git/volatility/vol.py -f capture.mem --profile=Win7SP1x86_23418 clipboard
Volatility Foundation Volatility Framework 2.6.1
Session WindowStation Format Handle Object Data
---------- ------------- ------------------ ---------- ---------- --------------------------------------------------
1 WinSta0 CF_UNICODETEXT 0x2a0163 0xffa007f8 GOLDEN Dany
1 WinSta0 CF_LOCALE 0x1c01fb 0xfe493690
1 WinSta0 CF_TEXT 0x1 ----------
1 WinSta0 CF_OEMTEXT 0x1 ---------- Gotcha!
Flag
Hero{PAVOLI-Ruben:GOLDEN-Dany:Nemesis-4.5.1}